A few weeks ago, a guide explaining how to install AWStats on FreeBSD was released here in adminbyaccident.com. On that piece a basic install of AWStats is shown, however, a nice and important functionality of AWStats is missing. Knowing the location of visitors is a matter of interest, for the sake of it or because […]

How to enable Geolocation in AWStats on FreeBSD 13.0
Linus on ZFS
Disclaimer: What you are about to read may contain inaccuracies. Feel free to discuss them somewhere else. This is also my opinion and as such it may change through time, maybe tomorrow, next month, next year, next decade or never. I do also make very few reviews (if any) of what I write here so […]

Microsoft’s Patch Tuesday – April 2020
For the first time here at adminbyaccident.com I will share some information about Windows patching that I hope can shed some light and help people on deciding what to patch and how quickly to patch. Digesting Microsoft’s Patch Tuesday releases is always tricky. The amount of information is overwhelming and since almost every company on […]
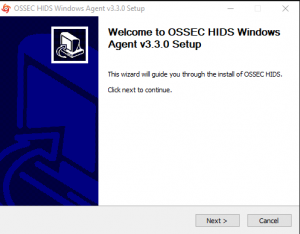
How to install OSSEC agents on Windows
On a recent post I published about how to install an OSSEC server on Ubuntu I explained how this solution can help secure an infrastructure by deploying agents which report back to a central server. This is the second part of this server-client story. On this guide you will read about setting up agents and […]
What is Expect?
Expect is a handy scripting tool for task automation. You may have never heard of it. I heard about many scripting things before. But one day I needed something simple but didn’t know how to proceed, what would be a good tool for my purpose. The task was simple. Exporting a website content from a […]
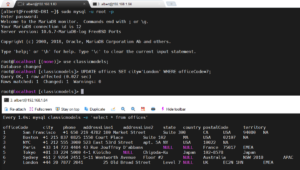
How to setup MariaDB master-slave replication on FreeBSD
Having all the data in just one server is not the best idea. Especially when talking about a database server. Spreading information in several boxes is a good measure to prevent data loss but also for performance. A MySQL/MariaDB master-slave replication scheme is often used as a good solution for both, data redundancy and speed. […]

How to mitigate Spectre and Meltdown on an HP Proliant server with FreeBSD
As recently announced in a previous article I wanted to write a couple of guides on how to mitigate Spectre and Meltdown vulnerabilities in GNU/Linux and UNIX environments. It is always a good and I hope a standard practice to have your systems patched and if they aren’t for whatever the reason (that legacy thing […]
The firewall
If you don’t know why you need a firewall it’s because you are not very tech savy. Don’t worry. You can discover by yourself why you need one. The router sitting in your house has one installed in it. And please don’t disable that by any mean. You can check why a firewall is important […]
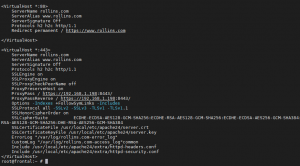
How to configure Apache HTTP with a TLS reverse proxy backend on FreeBSD
A few weeks ago I published a how to guide to configure Apache HTTP as a reverse proxy. On that ocasion I was following what the average guide on the internet does on Linux. A front end server with Apache HTTP on calls a backend server where the real site is sitting. Many backend calls […]
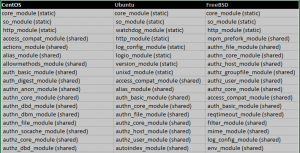
Reasonable amount of enabled modules on Apache HTTP
CentOS Ubuntu FreeBSD core_module (static) core_module (static) core_module (static) so_module (static) so_module (static) so_module (static) http_module (static) watchdog_module (static) http_module (static) access_compat_module (shared) http_module (static) mpm_prefork_module (shared) actions_module (shared) log_config_module (static) authn_file_module (shared) alias_module (shared) logio_module (static) authn_core_module (shared) allowmethods_module (shared) version_module (static) authz_host_module (shared) auth_basic_module (shared) unixd_module (static) authz_groupfile_module (shared) auth_digest_module (shared) access_compat_module (shared) […]