ARP spoofing attacks are quite harming and they can easily constitute a man-in-the-middle (MITM) attack. They consist on the attacker sending ARP packets into the network the victim is located, typically redirecting traffic to the attacker’s machine. Once this is achieved the attacker can sniff all the traffic sent by the victim’s device and obtain […]
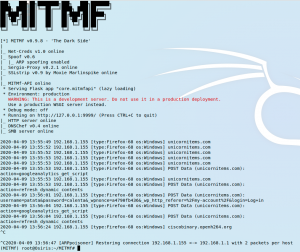
ARP spoofing attacks

How to upload a FreeBSD custom image on DigitalOcean
Due to DigitalOcean not releasing ready to use images for FreeBSD 13 at this time, and since I opened a ticket a couple of months ago without a strong positive message from DigitalOcean supporting FreeBSD 13, I’ve decided to make use of their custom image upload service and give it a go. I must say […]

FreeBSD Jails
The FreeBSD jails is a virtualization technology you may have skipped for too long. It is an operating system level virtualization and is one of the differential characteristics of FreeBSD from Linux. Solaris took it to the main corporate use with Zones and as it couldn’t be any other way the Illumos folks also play […]

How to manually update Letsencrypt certificates on FreeBSD
Update 05-2020: If anyone is interested on the automatic process you can read my tutorial on DigitalOcean about the topic. On this guide we will manually update our Letsencrypt certificate on FreeBSD for a single website. It is a simple operation that can be automated as a cron job, but seeing it is always informative […]

Abandon Linux. Jails for developers.
Reading the title you might think I want to put developers in Jail and although some may be good candidates this is in the far opposite of my intention. I am talking about FreeBSD Jails. For the unfamiliar with the concept those Jails are userland secure contained environments that share a common kernel. Purists and […]

How to enable TLS traffic from the origin server on Cloudflare Argo Tunnel
As it can be read in the last post, setting up a Cloudflare Argo Tunnel to serve web content from home or corporate network without poking holes to it, is quite easy to achieve. In this article I’ll show you how to enable TLS traffic from the origin server on Cloudflare Argo Tunnel. Obviously, you […]

How to setup a simple firewall in FreeBSD using IPFW
Setting the firewall up is a mandatory task on any computer facing the internet. This is a simple, straightforward how to article on how to setup a box with an easy firewall configuration on FreeBSD. If you find the articles in Adminbyaccident.com useful to you, please consider making a donation. Use this link to get […]
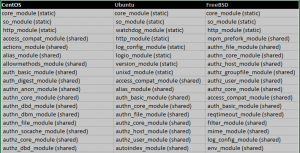
Reasonable amount of enabled modules on Apache HTTP
CentOS Ubuntu FreeBSD core_module (static) core_module (static) core_module (static) so_module (static) so_module (static) so_module (static) http_module (static) watchdog_module (static) http_module (static) access_compat_module (shared) http_module (static) mpm_prefork_module (shared) actions_module (shared) log_config_module (static) authn_file_module (shared) alias_module (shared) logio_module (static) authn_core_module (shared) allowmethods_module (shared) version_module (static) authz_host_module (shared) auth_basic_module (shared) unixd_module (static) authz_groupfile_module (shared) auth_digest_module (shared) access_compat_module (shared) […]

How to enable Geolocation in AWStats on FreeBSD 13.0
A few weeks ago, a guide explaining how to install AWStats on FreeBSD was released here in adminbyaccident.com. On that piece a basic install of AWStats is shown, however, a nice and important functionality of AWStats is missing. Knowing the location of visitors is a matter of interest, for the sake of it or because […]
Linus on ZFS
Disclaimer: What you are about to read may contain inaccuracies. Feel free to discuss them somewhere else. This is also my opinion and as such it may change through time, maybe tomorrow, next month, next year, next decade or never. I do also make very few reviews (if any) of what I write here so […]